Quick take:
- There is a new NFT exploit on OpenSea.
- According to the phishing scam detection tool Pocket Universe, the exploit targets NFTs listed before May 2022.
- The exploit capitalises on a loophole that allowed proxy contracts to withdraw NFTs from the previous version of OpenSea that used the Wyvern Protocol.
Scammers are at it again on OpenSea. A new exploit that targets non-fungible tokens listed before May 2022 has been spotted. Explaining how the exploit works via a Twitter thread, phishing scam detection tool Pocket Universe said cybercriminals are taking advantage of a loophole created when OpenSea used to use Wyvern Protocol.
The leading NFT marketplace updated to Seaport Protocol in May adding more features to the bidding process. However, not everyone migrated their collections to the new protocol, with some NFTs still listed on the old version.
In the previous version, upon listing an NFT on OpenSea, users gave a proxy contract the right to withdraw their NFT, based on the SetApprovalForAll permission.
According to Pocket Universe, “this new exploit tricks you into signing a transaction that gives the attacker ownership of your proxy contract, thus giving them permission to withdraw your NFTs.”
Users can avoid falling into the trap by following three simple steps. The first step is to check the transaction carefully to ensure there are no red flags like statements prompting you “to upgrade”.
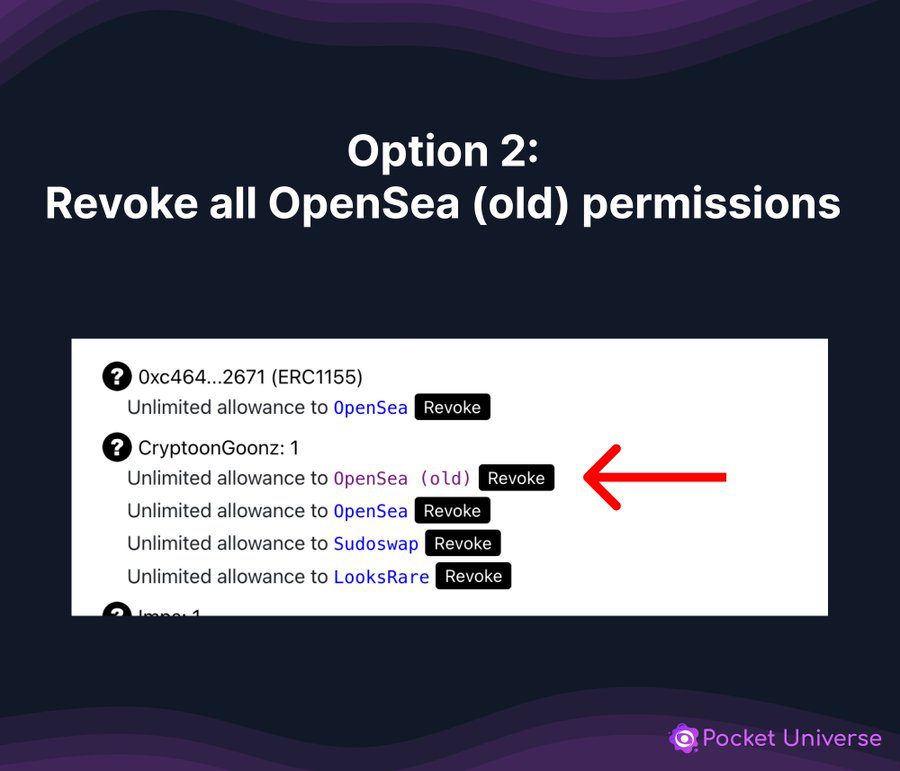
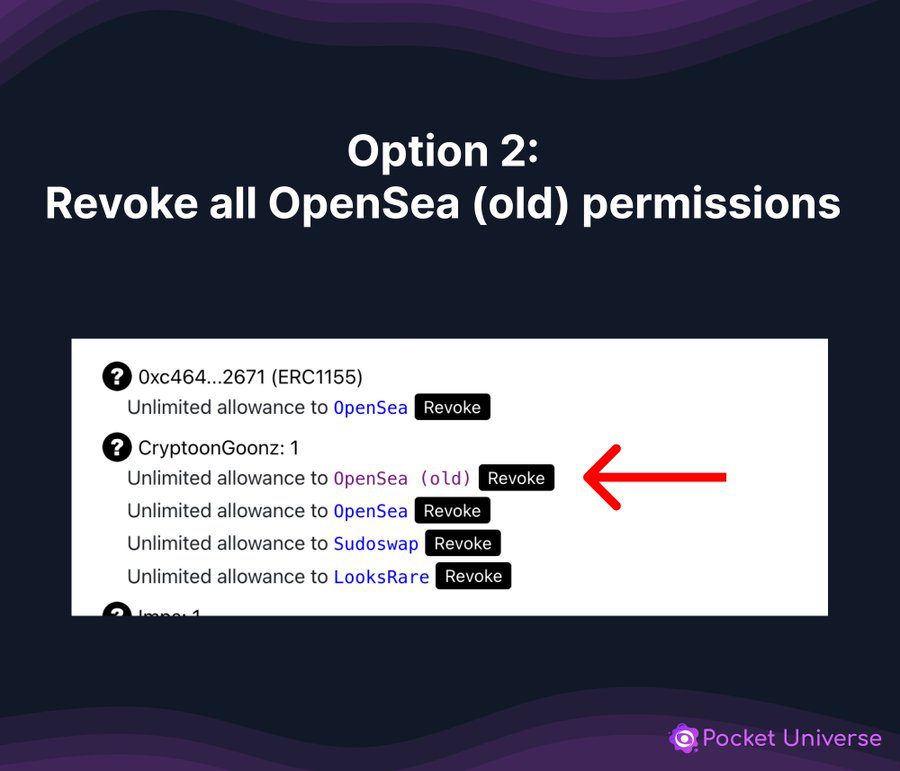
The second step involves visiting RevokeCash, a cross-chain interoperability protocol for managing NFT transactions. The tool prevents users from being exposed to scams on more than 30 blockchains including Ethereum, Polygon and Avalanche, among others.
Once you arrive at the platform, you’ll need to revoke permissions to OpenSea, the old version. The downside to doing this is that you will still incur gas fees for each collection revoked, but the proxy contract will be barred from draining your assets.
The third option is using Pocket Universe’s scam detection tool, which can be added to your browser as an extension. The tool issues a red warning via a pop-up message when you come across the exploit.
Stay up to date:





