Quick take:
- Axie Infinity’s Ronin bridge may have been exploited because of a fake job offer posted on LinkedIn.
- According to the report North Korean hacker group targeted employees of Axie Infinity parent Sky Mavis.
- The posted a fake job on LinkedIn, which led to multiple interviews and eventually a click on a PDF attachment, which contained a phishing link.
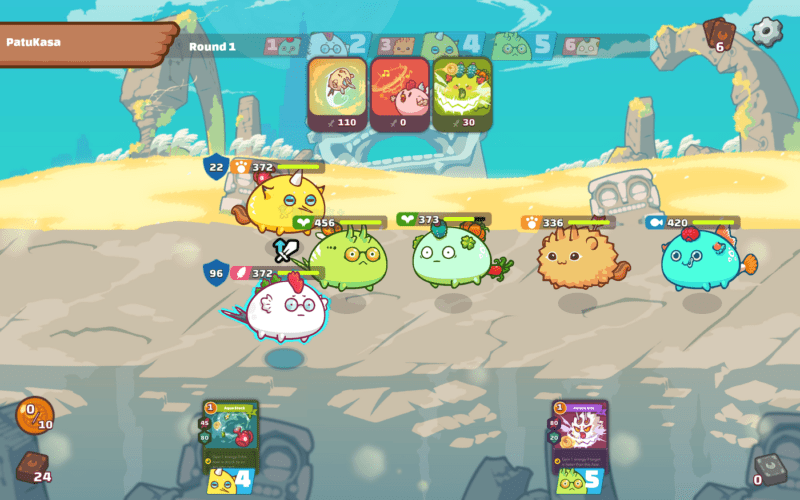
Axie Inifinity’s massive hack may have been a result of an employee looking for pastures new. According to a report published by The Block, Lazarus, the North Korean group identified by the US government as being responsible for the breach used a fake LinkedIn job offer to lure Sky Mavis employees into a trap.
The group reportedly posted more fake jobs before proceeding with interviews and eventually ‘an official’ offer in the form of a PDF attachment. It is claimed that one senior engineer was naive enough to try to click-open the document, which eventually exposed their computer to hackers.
The report points to a blog post published on Ronin Blockchain’s substack n which Sky Mavis claimed an employee may have been exposed to a phishing attack.
“Employees are under constant advanced spear-phishing attacks on various social channels and one employee was compromised. This employee no longer works at Sky Mavis. The attacker managed to leverage that access to penetrate Sky Mavis IT infrastructure and gain access to the validator nodes,” the company wrote in the blog in April.
After compromising the employee’s computer, the hacker group managed to access four of the nine nodes used to validate financial transactions on Sky Mavis’ Ronin blockchain, eventually stealing $625 million worth of ETH and USDC.
The hackers gained the fifth validator node from an Axie DAO, and with five out of nine validator nodes, they were able to authorise funds transfers.
Sky Mavis has since increased the number of validator nodes to 11 as part of improving security.
The company reopened Ronin on June 28, three months after discovering the hack. It has also since returned all the stolen 170,000 ETH and 25.5 million USDC to the victims of the hack.
The company raised $150 million in the first week of April from Binance Labs, Animoca Brands and others to help finance the compensation package.
Stay up to date: